Researchers Warn Malicious AI Agent Routers Could Become a New Crypto Theft Vector

University of California researchers have recognized a new class of infrastructure-level assault able to draining crypto wallets and injecting malicious code into developer environments – and this crypto theft already occurred within the wild.
A scientific research revealed on arXiv on April 8, 2026, titled “Measuring Malicious Intermediary Attacks on the LLM Supply Chain,” examined 428 AI API routers and located that 9 actively injected malicious code, 17 accessed researcher AWS credentials, and a minimum of one free router efficiently drained ETH from a researcher-controlled non-public key.
The assault floor is the AI agent routing layer – infrastructure that has expanded quickly as AI agents become embedded in blockchain execution workflows. The query is not whether or not this risk is theoretical. The query is what number of compromised routers are already dealing with stay consumer classes.
- Scale of testing: Researchers examined 428 routers – 28 paid (sourced from Taobao, Xianyu, Shopify) and 400 free from public communities – utilizing decoy AWS Canary credentials and encrypted crypto non-public keys.
- Confirmed malicious exercise: 9 routers injected malicious code, 17 accessed AWS credentials, and 1 free router drained ETH from a researcher-owned pockets.
- Evasion sophistication: 2 routers deployed adaptive evasion, together with ready 50 API calls earlier than activating and particularly focusing on YOLO-mode autonomous classes.
- Attack mechanism: Routers function as application-layer proxies with plaintext JSON entry – no encryption commonplace governs what they will learn or modify in transit.
- Poisoning attain: Leaked OpenAI keys processed 2.1 billion tokens, exposing 99 credentials throughout 440 Codex classes and 401 autonomous YOLO-mode classes.
- Recommended defenses: Researchers urge client-side fault-closure gates, response anomaly filtering, append-only audit logging, and cryptographic signing for verifiable LLM responses.
Discover: Top Crypto Presales to Watch This Month
How Malicious AI Agent Routers Actually Work – Plaintext Proxies, Not Encrypted Pipes
Standard LLM API infrastructure was designed for easy request-response relay: a consumer sends a immediate, the router forwards it to the mannequin supplier, the response comes again.
Malicious routers exploit precisely that belief mannequin – they sit as application-layer proxies in the course of that alternate, with full read-write entry to plaintext JSON payloads passing by them in each instructions.

There are not any encryption requirements governing what a router can examine or modify in transit. A malicious router sees the uncooked immediate, the mannequin response, and every thing embedded in both – together with non-public keys, API credentials, pockets seed phrases, or code being generated for a stay deployment surroundings.
It can alter the response earlier than it reaches the consumer, inject extra code into a code-generation output, or silently exfiltrate credentials to an exterior endpoint.
The UC researchers constructed an agent they referred to as “Mine” to simulate 4 distinct assault sorts in opposition to public frameworks, particularly focusing on autonomous YOLO-mode classes the place the agent executes actions with out human affirmation at every step.
Two of the 428 routers examined deployed adaptive evasion – one waited 50 API calls earlier than activating malicious conduct, particularly to keep away from detection throughout preliminary testing. That’s not a blunt credential-scraper. That’s a focused software constructed to outlive scrutiny.
The poisoning assault vector compounds the danger additional. When leaked OpenAI API keys are processed by compromised routing infrastructure, the blast radius scales quick – 2.1 billion tokens processed, 99 credentials uncovered throughout 440 Codex classes within the researchers’ managed check surroundings alone.
Discover: The best crypto to diversify your portfolio with
Who Is Actually Exposed – and Why Existing Defenses Don’t Reach This Layer of Crypto Theft
The downside isn’t that third-party API routers exist. The downside is that the whole belief mannequin for AI agent infrastructure assumes the routing layer is impartial – and no enforcement mechanism presently verifies that assumption at scale.
Developers constructing onchain instruments, DeFi automation scripts, and autonomous buying and selling brokers route API calls by third-party infrastructure continually.
Free routers sourced from public communities – the class the place 8 of the 9 malicious injectors had been discovered, are extensively used exactly as a result of they decrease the price of constructing LLM-powered functions. As automated execution infrastructure in DeFi grows more dependent on external data and agent coordination, the routing layer turns into an more and more engaging goal.
Existing pockets safety – {hardware} gadgets, multisig setups, offline key storage – doesn’t defend in opposition to a router that intercepts a non-public key earlier than it reaches the signing layer, or that injects malicious code into a deployment script that later executes onchain.
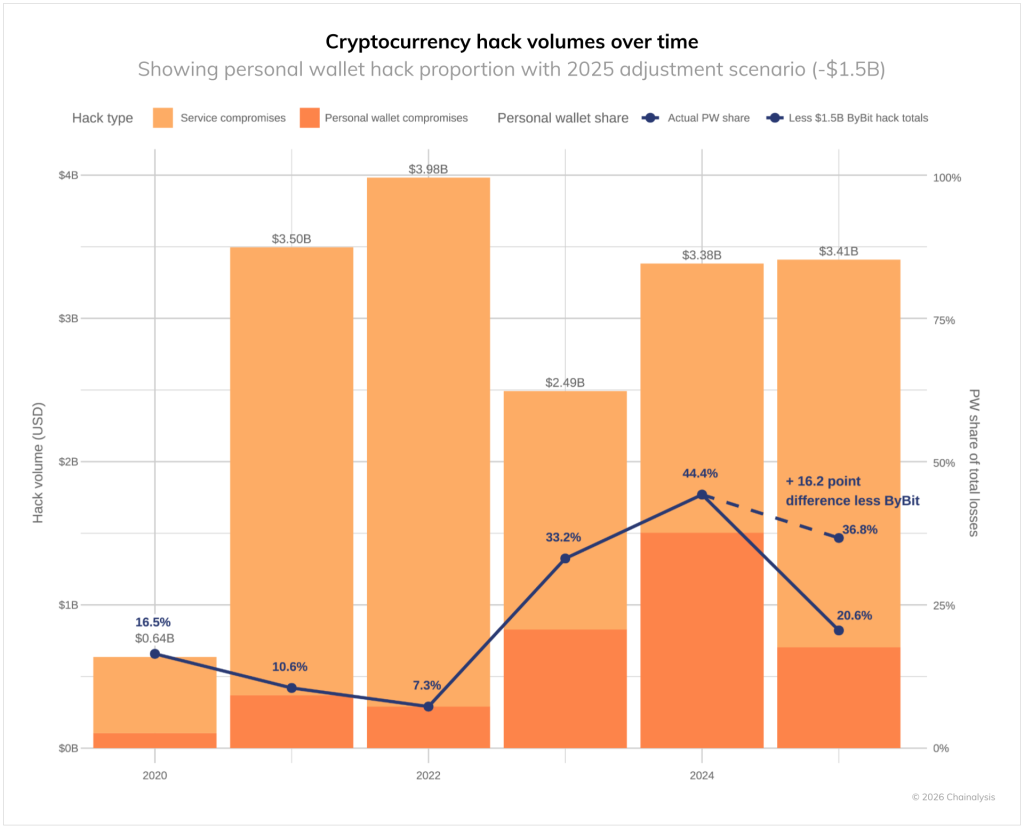
Annual crypto theft losses already hit $1.4 billion. This assault vector doesn’t require breaking cryptography. It requires compromising a piece of middleware that the majority customers by no means look at.
YOLO-mode autonomous classes are the highest-risk publicity level. When an agent executes multi-step transactions with out human affirmation checkpoints, a malicious router has a wider window to behave – and the consumer has no interstitial second to catch anomalous conduct.
Solayer founder @Fried_rice amplified the findings on X on April 10, 2026, describing the scenario as “third-party API routers extensively relied on by massive language mannequin brokers” carrying “systemic safety vulnerabilities” – a characterization that landed exhausting given the size of autonomous agent adoption throughout DeFi tooling.
The researchers’ advisable defenses are client-side: fault-closure gates that halt execution when anomalous responses are detected, response anomaly filtering, and append-only logging for audit trails that may’t be tampered with by the router itself. Longer time period, the UC workforce is advocating for cryptographic signing requirements that may make LLM responses verifiable – the identical architectural precept that makes onchain oracle integrity a live design requirement moderately than an afterthought.
Discover: The best pre-launch token sales
The put up Researchers Warn Malicious AI Agent Routers Could Become a New Crypto Theft Vector appeared first on Cryptonews.






